![]()
![]()
![]()
Use LEFT and RIGHT arrow keys to navigate between flashcards;
Use UP and DOWN arrow keys to flip the card;
H to show hint;
A reads text to speech;
83 Cards in this Set
- Front
- Back
|
Network |
A ______ is the combination of hardware, software, and connecting links that transport data |
|
|
PAN |
From a geographic perspective, networks can be classified as a LAN, ___, NAN, MAN, or WAN. |
|
|
Static |
Each host computer has an easy-to-remember domain name that translates directly to the computer's ____ IP address. |
|
|
Bandwidth |
_____determines how fast data travels to your computer from the Internet |
|
|
Mapping |
Drive ____ assigns a drive letter to a computer, storage device, or folder located on a network computer |
|
|
WiFi |
A public _____ network is a wireless LAN that provides open Internet access to the public in places such as bookstores, coffee shops, airports, hotels, and airports |
|
|
Modem |
A _____ is a device that makes it possible to send and receive data over telephone lines |
|
|
Intel |
_____ is the leading technology for wired networks; it is also included in some printers and other peripheral devices |
|
|
Bluetooth |
______ is a short range wireless network technology that is designed to make its own connections between electronic devices, without wires, cables, or any direct action from a user |
|
|
Peer-to-peer (p2p) |
Networks that use the _____ structure do not have a server |
|
|
Fidelity |
A popular technology for wireless network is Wi-Fi, which stands for wireless _____ |
|
|
Wired |
Data travels faster on ______ networks than on wireless networks |
|
|
Server |
A network ______ is a computer that provides services and distribute to resources to other computers on the network |
|
|
MAC |
A ______ address is a physical address, a unique number assigned to a computer when it is manufactured |
|
|
IP |
A(n) ______ address is a series of numbers used to identify a network device in virtually every type of computer |
|
|
Digital |
DSL (_____ subscriber line) is a high-speed, always on internet access technology that uses standard phone lines to transport data |
|
|
Domain |
The database that keeps track of the names that correspond to IP addresses is called the _____ name system |
|
|
Voice |
_____ over IP refers to a technology that uses an internet connection to place telephone calls instead of the regular phone system |
|
|
Radio |
A wireless network uses ______ waves, not cables, to send data from one node to another |
|
|
Com |
The top-level domain _____ is primarily for use by businesses |
|
|
Documents |
The Web is a collection of ____ that can be related by links |
|
|
HTML |
______ is the original markup language that specifies have a web document should appear printed or displayed on a computer screen |
|
|
An ActiveX control |
You can identify a secure website if you visit the website and your browser displays any of the following elements in the address bar, except: |
|
|
Browser |
A Web _______ is a software program that runs on your computer and helps you access web pages |
|
|
404 |
When a broken link points to a nonexistent HTML documents your browser typically produces a ______ Page Not Found error |
|
|
Certificate |
A digital ______ is a specifically coated electronic attachment to a file that verifies the identity of the file's source |
|
|
Flash player |
A plug-in, such as _____, is a program that lets a browser display a particular file format |
|
|
Status code |
Each of the following is a navigation tool available in a typical web browser, except: |
|
|
Status |
A web server's response to a browser's request includes a _______ code that indicates whether or not the browser's request can be fulfilled |
|
|
Keywords |
Most search engines work with queries in which you enter 1 or more words called, search terms or ____ |
|
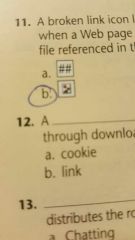
Circle, square, Triangle |
A broken link icon looks like _____ and occurs when a webpage link cannot find the file, URL, or graphic file referenced in the link |
|
|
Podcast |
A ______ is an audio file that is distributed through downloads or the use of a feed |
|
|
BitTorrent |
_______ is peer to peer file sharing protocol that distributes the role of file servers across many computers |
|
|
Links |
_______ allow web pages to become more interactive and to incorporate activities that would otherwise require a computer program, such as to enable ecommerce sites to verify credit card information |
|
|
Download it for free |
The typical way to get a plug in applications, such as the Adobe Reader, is to _____ |
|
|
E-commerce |
________ is the broad term used to describe all shopping for goods and services over the Internet |
|
|
Script |
An HTML _______ is a series of program instructions that can be embedded directly into the text of an HTML document |
|
|
Metasearch engines |
Some search sites use ________ to employ a series of other search engines and compile the search results |
|
|
NOT |
When creating a Boolean search, the minus sign (-) can be used in some search engines instead of the word |
|
|
Https:// |
Web pages that provide a secure connection start with ______ |
|
|
UPS |
Is a device that provides can a continuous supply of power during a power failure and prevents spikes and surges from reaching your computer |
|
|
Power strip |
Contains multiple outlets that can not filter out power spikes and surges |
|
|
Password |
Is a series of characters that a user creates to identify his or her user ID |
|
|
Malware |
Is malicious code designed to disrupt a computer's normal operation |
|
|
Biometrics |
A method of personal identification, called _____, bases identification on a physical trait. |
|
|
Firewall |
Is software or hardware designed to filter out suspicious data attempting to enter or leave a computer |
|
|
Virus |
A computer _____ is a program that reproduces and attaches itself to a file so it can spread from file to file |
|
|
|
A spam filter will help you avoid unwanted _____ |
|
|
InPrivate |
Browsing feature in Internet Explorer keeps the browser from storing any data |
|
|
Denial of service |
A _______ attack floods network servers with useless traffic |
|
|
Cookie |
A message containing information about the user sent from a web server and stored on the hard drive |
|
|
Zombie |
A computer controlled by a bad bot is called a ______ |
|
|
Intelligent agent |
Is software that can automate a task when given a command |
|
|
Surges |
Power ______ can damage sensitive computer parts |
|
|
PIN |
A password uses a combination of letters and numbers but a _____ only uses numbers |
|
|
Blended |
Virus experts use _____ threat to describe threats that combined for more than one type of malicious program |
|
|
Signature |
A virus ______ is a section of program code used to identify a known a malicious program |
|
|
Phishing |
Is an email based or IM scam designed to persuade you to reveal confidential information |
|
|
Full |
A ______ backup contains a copy of every program, data, and system file on a computer |
|
|
Boot disk |
Is a removable storage medium containing the files needed to start your computer without accessing the hard drive |
|
|
Scanner |
A ____ digitizes printed images |
|
|
MIDI |
Specifies a standard way to store music data for synthesizers, electronic instruments, and computers |
|
|
Resolution |
Is expressed as the number of horizontal and vertical pixels that the grid of a bitmap graphic contains |
|
|
Bitmap |
A _____ graphic is resolution dependent, which means that the quality of the image relies on its resolution |
|
|
Depth |
Color _____ refers to the number of colors available for use in a bitmap graphic |
|
|
Palette |
Color ____ hold the section of available colors and allows you to select a group of colors to use for a bitmap graphic |
|
|
Vector |
A ____ graphic contains the instructions that a computer needs to create the shape, size, position, and color for the graphic |
|
|
Synthesis |
Speech ____ is the process by which Computers produce sound that resembles spoken words |
|
|
Sampling |
______ rate refers to the number of times per second that a sound is collected or measured during the recording process, and it is expressed in Hertz (Hz) |
|
|
Tracing |
Ray ______ is the process of adjusting the colors in a rendered image to coincide with the highlights and shadows that would be produced by a light source |
|
|
Streaming |
_____ video plays the video while continuing to receive it |
|
|
Graident |
Is a smooth blending of shades from one color to another or from light to dark |
|
|
Compression |
File _____ Software is a utility program that allows you to manually reduce the size of files |
|
|
Codec |
A _____ compresses a video stream when a video is stored and decompresses the file when the video is played |
|
|
Analog |
Audio can be _____, digital, or synthesized |
|
|
Pixel |
Each _____ in a picture is a find a color, which is stored as a binary number in a file |
|
|
Codec |
You can transfer images from a digital camera to a computer using any of the following EXCEPT a ____ |
|
|
Scanner |
Which of the following devices is never used to capture a digital video? |
|
|
Audio |
AAC, AIF, MP3, Wave, and WMA are formats for which types of files? |
|
|
Graphics |
RAW, gif, tif, jpeg, and bmp are all formats for which types of files? |
|
|
Reord= row Field= column |
In access, what does record and field mean? |
|
|
Link between tables |
What is a relational database? |
|
|
Table |
Collection of many records |

